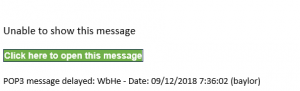
The scam where you get an email that appears to come from your supervisor, dean, or another higher up at the university is not slowing down. The most common spoofed individuals are the University President, the Dean of the Law School, & the Athletic Director, but the scammers are also imitating department heads & others as well. In the case of these emails, please forward them to ITS via the Help Desk or abuse at baylor dot edu so that we can block that email address from sending to or receiving email from Baylor addresses. There is no danger to your system or the individual’s system that they are imitating as no actual hacking or unauthorized access has occurred.
Some tips to determine that the email is a scam:
- the email is short, usually one or two sentences & it lacks proper spelling, grammar, capitalization, and/or punctuation
- the sender’s email address may display the proper Baylor email address of the individual they are imitating, but if you right click & select ‘Open Contact Card’ or click the Reply button the actual address that you will see will NOT be an @baylor.edu email address
- the sending email address might include baylor.edu but it will NOT be after the @ symbol, meaning it is NOT a Baylor email address
- the scammers are copying signatures to make the email seem legit, so always verify the email address before replying
- if they ask you to purchase gift cards for any reason & to send them the codes from the back of the gift cards, cease communication immediately & contact the Help Desk so that ITS can block that email address from communicating further with Baylor employees